Specializations
Some of Our Areas of Expertise
We work with a lot of different industries, and despite the varied products, services, missions, and objectives they each have, we constantly find ourselves working with organizational leadership to address the same types of fundamental challenges.
At Centripetum, our agnostic approach to addressing governance, risk and remediation, and cybersecurity means we don’t walk in with preconceived notions of how your organization should be organized, operate, or change. We understand that the way to find your center will be unique. We take the time to understand what you need and what you want, and then help you to develop processes and find solutions that work for your organization and your people.
Yes, we have turn-key solutions and rapid-response plans, which means that – with the full engagement of your team – we can help you reach minimum or mandatory levels of compliance or security in weeks, not months or years. However, we never force our clients into some one-size-fits-all “program” that far too many consultants and security service providers do today.
We have PRIOR or ACTIVE experience in the following industries, programs, and initiatives (CLICK OR SCROLL for details):
- Defense Industrial Base / Department of Defense Contractors
- Education / K-12, Colleges, and Universities
- Financial Sector / Banks and Credit Unions
- Electricity Sector (especially subject to NERC CIP)
- Federal Government Systems / Assessment and Authorization (A&A)
- Governance of IT and Information Security Programs / COBIT, ISO 20000, ISO 27001, ITIL
- Natural Gas Pipeline and Facility Security
- Privacy and Data Loss Prevention (DLP)
- Regulatory Compliance / International, Federal, and State Laws
- Transportation Systems / Passenger and Freight Railroad Carriers
- Water Sector / Public Water Systems (PWS)
Defense Industrial Base (DIB)
DIB contractors and sub-contractors with CUI are presently required to be fully compliant with NIST SP 800-171 (per DFARS Part 252.204-7012), and yet more than 80% of contractors surveyed by the federal government acknowledged unacceptable levels of non-compliance and substandard DoD SPRS scores.
We know that CMMC is a real concern for many businesses, and the Federal government will approve and implement it… eventually. For most businesses, though, it’s “the cart before the horse”. It will be impossible for your business to meet and pass the stringent auditing standards of CMMC until you first establish a managed and repeatable program of basic security controls and compliance oversight under the existing 800-171 requirements.
We help you to build or enhance your programs to ensure that you don’t just become compliant, but stay compliant. We provide managerial direction, operational directives, and technical know-how to become compliant.
Most importantly, we know how to do it because we have to do it ourselves.
Get REAL Answers and PRACTICAL Advice...
Read our FCI, CUI, and CMMC Discussion, where we do away with the hype, scare tactics, technical jargon, and information overload to help you understand exactly what you need to be doing yesterday, today, and 6 months from now.
Education / K-12, Colleges, and Universities
So many competing interests, so little budget and expertise. We’ve been there, literally (our CEO is a former college professor).
K-12 must juggle shrinking budgets, an increasingly competitive market for talent, conflicting interests of parents-with-educators, parents-with-administrators, educators-with-administrators, parents-with-other-parents, etc… while remembering the thousands of inquisitive minds getting older and wiser each day, learning and prepared to test the boundaries of every rule, roadblock, and barrier put in place. It can seem hopeless, but it isn’t. And we can’t fix it all, but we’ll help where we can.
We work to create layered, segmented, and enclave architectures that allow your seemingly conflicted IT needs and requirements can work together. We help to develop strategies that ‘thread the needle’ between open access to information that encourages learning and critical thinking, while addressing the need to protect and secure certain information from unauthorized access.
Meanwhile, the deadline for colleges and universities to fully comply with the GLBA Safeguards Rule 2023 (16 CFR Part 314) is just around the corner, but we also know that the complexity and unusual nature of college and university campuses and schools continues to create complicated webs for addressing compliance regulations. We have the experience of addressing ‘difficult’ IT infrastructures and establishing secure and controlled network segmentation while respecting the historical and inherent open nature of academia.
Electricity Sector
The safety and stability of the electrical grid is vital to the economic success of a community. We work with investor-owned utilities, municipal services, cooperatives, generation, transmission, and distribution providers and other electric sector entities to establish secure and ensure compliance with NERC CIP and various state laws.
For example, we have the distinction of having built a complete NERC CIP compliance program for multi-state generation from the ground up. We took one IOU from less than 10% compliance to 98% compliance in just a few short years. We’ve re-built programs to work for control centers and transmission, too. We’ve been on the ground implementing solutions in DCS and SCADA environments, while working with executive teams to re-align organization priorities that embrace compliance, establish expectations (and accompanying policies), and actively enforce compliance (and non-compliance).
The electricity sector has the distinction of being a leader in industrial cybersecurity initiatives, but it is facing new challenges. More sophisticated risk management programs continue to develop and expand. Increased scrutiny is coming not just from regulators any more, but directly from federal and state legislative and executive concerns. New cybersecurity demands on fuel supply chains (see below) will require better alignment between disparate industries, while a move from fossil fuels and a push towards the use of more electricity in homes, vehicles, and businesses will put additional upward pressure on the security (e.g., reliability) of the grid.
What’s your challenge? Let’s tackle it together.
Federal Government Systems / Assessment and Authorization (A&A)
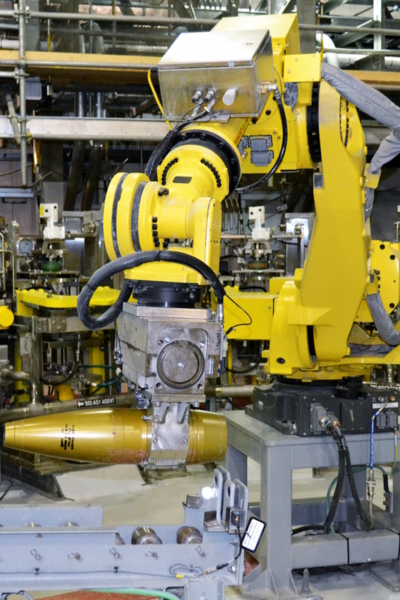
We like a good challenge. We built a cybersecurity program from the ground up that became the FIRST ‘industrial control system’ under the Department of Defense to receive an A&A. Think it’s hard to become compliant for an OTS IT network? Try a distributed SCADA system surrounded by robotics, machinery, and rooms with deadly chemicals unfit for human cohabitation.
In these changing times, the proper implementation of risk management and cybersecurity in Federal systems can be a particular challenge: striving to simultaneously protecting national interests while still providing an adequate level of operational transparency that ensures its citizens have faith and trust in the activities of their government. No one ever said democracy was easy.
From public offices and environmental labs to cleared facilities (FCLs) and military bases, we’ve been there to understand that government systems can be… challenging. Our objective is to ensure that a system receives its A&A while also incorporating best practices and the latest techniques in oversight and control.
An example: building a bigger/stronger wall is not always the answer. We know from military experience that, rather than trying to absorb the entire blast of an attack, it’s sometimes wiser to disperse the force around and away, sacrificing non-critical elements to protect the critical. Smart design (especially with older systems) can actually let those systems fall over gracefully when the worst types of attacks and damage occur, but still have proper resilience to recover quickly with minimal disruption.
Financial Sector / Banks and Credit Unions
Where do you even begin?
FFIEC, GLBA, SOX, PCI-DSS, BSA, FINRA, NCUA and 12 CFR 748/749… banks and credit unions have cybersecurity directives coming at them from every direction. We know your situation too well (our CFO has worked and managed in banks and credit unions).
At Centripetum we’ve worked with financial institutions large and small, even little credit unions that could count their staff on two hands. Your size doesn’t matter, because the laws and regulations don’t care, either. The daily grind is enough to have all hands on-deck, but then to deal with technical and operational requirements that most financial staff are not experts at is… daunting.
By way of example, we take pride in having built a compete cybersecurity program from the ground up for a small community credit union struggling without the know-how or the resources to hire high-priced “banking” consultants (who they were told they would need)… and see them go from years of non-compliance and threatened actions (and stacks of DORs) by the NCUA, to universal praise from their examiners.
We know how resource allocations in financial institutions really work; we know how much non-compliance puts pressure on the institution and mentally drags on its dedicated employees; we know how much you really want to protect your company and its stakeholders. And we want to help you succeed.
Governance of IT and Information Security Programs
Successful companies don’t just “wing it” when it comes to planning, coordinating, and running their IT, risk management, and cybersecurity programs.
COBIT, ISO 22000, ISO 27001, ITIL… Governance models help to create proper distinctions and better alignment between the roles of governance (strategies) and management (operations). They serves to break the cycle when employees are left trying to figure out how things should work, management and executives assume they can just keep shoveling new ideas, directives, and work down the well and it will all just magically ‘get done’, and no one understands why nothing gets done.
Don’t get us wrong: implementing these models properly (which we find is often not the case) is hard, and starting down the path typically starts with everyone admitting to their failures and start actively listening to everyone else… but the end result is amazing. When we’ve implemented these models some concrete changes we find include:
- It empowers everyone to be able to say “NO” when the processes are not followed!
- The Board is given honest/realistic expectations; the Board has to give realistic directives
- Executives must prioritize (organization-wide) and budget (no unfunded mandates) new IT initiatives and resource-heavy projects
- Managers have clearer direction on the use of resources, but also greater accountability for outcomes
- Employees rate higher job satisfaction with clearer work requirements and adequate resources for each task
- Critical business obligations – like cybersecurity and regulatory compliance – stop getting treated as “projects” or one-time costs
Natural Gas Pipeline and Facility Security
The TSA’s most recent issuance of security directive Pipeline-2021-02D (SD02D) continues to be a significant cybersecurity initiative for the owner/operators of hazardous liquid and natural gas pipelines or liquefied natural gas facilities (if notified by the TSA that your system or facility is critical).
But our pipelines must be protected: with the nation’s shift towards natural gas for baseload electric generation, natural gas becomes even more important to heating, cooling, and energizing our economy. Weighing this with all the life-critical functions that depend on reliable electricity, and the natural gas supply chain becomes one of our most vital assets.
We help you to understand your Operational technology (OT) environment and create security programs and solutions that provide the right protections, while ensuring your ability to continue delivering value to your stakeholders. At the same time, we understand the regulatory landscape and we focus on making sure that you have both functional security and regulatory adherence that meets the TSA’s performance-based measures and expected outcomes.
We will work to ensure that you:
- Establish and implement a TSA-approved Cybersecurity Implementation Plan
- Develop and maintain an up-to-date Cybersecurity Incident Response Plan to reduce the risk of operational disruption, or the risk of other significant impacts on necessary capacity
- Establish a Cybersecurity Assessment Program and an annual plan that describes how you will proactively and regularly assess the effectiveness of your cybersecurity measures and identify and resolve system vulnerabilities
Privacy and Data Loss Prevention (DLP)
We’re not lawyers, we’re better.
After all, you usually hire a lawyer after you’ve been sued.
We work to keep you from being sued in the first place.
Consider for a moment:
- Each state (and territory) in the U.S. has it’s own privacy and/or cybersecurity laws.
- Even if you’re a ‘company of one’, you are still on the hook to follow each state’s laws if you have any working relationship with a citizen of that state.
- And it gets worse if any customer or employee is a citizen of or residing in a foreign country: you’re beholden to their laws, too.
- No, it does NOT matter where your company is based… you are not exempt.
And no, you did not read any of that incorrectly. Privacy is serious business, and most companies today are being sued not for the actual cybersecurity breach or loss of data, but because they failed to act and notify affected people in a timely manner.
At Centripetum we explain to you what the laws are trying to accomplish, what you will generally need to do (per the law) to be compliant, and then develop strategies and the operational programs to ensure that you are protecting the privacy of people’s sensitive information in your possession, and have a rapid-response program ready to execute when it occurs.
“Wait… you said WHEN, not IF!” Well its nearly certain, but that is a whole other discussion…
Regulatory Compliance
Adhering to federal and state regulations can seem like a daunting – and thankless – task… especially for small business who either don’t have the experience or the staff to wade through it all. But we deal with regulatory compliance EVERY DAY, and we’ve made it one of our company’s most in-demand services: “taking that bag of snakes and laying them out straight”.
Addressing regulatory compliance is a six-step process (some of the steps are easier than others):
- Read and understand the regulations your organization is subject to
- Read and understand the standards those regulations call upon for you to follow (if applicable)
- Write and formally adopt policies that say you and your employees acknowledge an understanding of and will commit to following those regulations
- Write operational procedures that describe any and all work processes that implement the policies and requirements of the standards/regulations
- Create processes and oversight that ensure those processes are repeated and repeatable (think ‘quality control’ for compliance)
- Establish a culture of compliance and consistent auditability – accept and embrace that your compliance is subject to constant scrutiny… because it is
We don’t just advise you at each step, we’ll work with you to ensure the writing, documentation, work processes, backend processes, and compliance frameworks are all in place. We can even help you with the work itself, if that’s what it takes to get you – and keep you – compliant.
Transportation Systems / Passenger and Freight Railroad Carriers
The TSA’s issuance of Security Directive 1580/82-2022-01: Enhancing Rail Cybersecurity has created new challenges for the rail industry, but we can help.
With years of experience securing industrial control systems (ICS) – especially DCS and SCADA designs – we can help you to understand your Operational technology (OT) environment and create security programs and solutions that provide the right protections for one of our nation’s most important critical infrastructure, while ensuring the ability to continue delivering value to your stakeholders and customers without adverse impacts to operations. We understand the requirements and we focus on making sure that you have both functional security and regulatory adherence that meet the TSA’s performance-based measures and expected outcomes.
We will work to ensure that you:
- Identify your key systems that, if compromised or exploited, could result in operational disruption
- Develop segmentation policies and controls to ensure that your OT systems can continue to safely operate in the event that your IT systems are compromised, and vice versa
- Create access control measures to secure and prevent unauthorized access to key systems
- Implement continuous monitoring and detection policies and procedures to detect cybersecurity threats
- Implement a risk-based security patch management strategy
Water Sector / Public Water Systems (PWS)
The Environmental Protection Agency (EPA) has taken action with ALL public water systems (PWS) under the recent memorandum, “Addressing PWS Cybersecurity in Sanitary Surveys or an Alternate Process“. The goal is absolute, especially in the face of so many recent threats and events: protect the supply and safety of water provided to customers, and minimize the impacts of threats and attacks when they occur.
As a PWS you must have a documented cybersecurity program with technical and administrative controls to protect your operational technology (e.g., SCADA), and the States must include it in their sanitary surveys or other assessments. Note that this interpretation applies to all PWSs, and not just the subset that was previously subject to the America’s Water Infrastructure Act of 2018 (AWIA).
So how can we help?
- Develop your self-assessment or perform a required third-party assessment (per state rules)
- Identify and address your cybersecurity gaps and weaknesses
- Built new or reinforce your existing cybersecurity program
- Identify adequate and practical technical and administrative controls
- With your team we’ll implement controls, update operations, and built the culture
The EPA already provides a number of resources on Cybersecurity for the Water Sector. We’re here when you’re ready to do the ‘heavy lift’, though, to start putting it all together and fully integrating cybersecurity into your business operations.